
The threat actor behind the RomCom RAT (remote access trojan) has refreshed its attack vector and is now abusing well-known software brands for distribution.
In a new campaign discovered by BlackBerry, the RomCom threat actors were found creating websites that clone official download portals for SolarWinds Network Performance Monitor (NPM), KeePass password manager, and PDF Reader Pro, essentially disguising the malware as legitimate programs.
In addition, Unit 42 discovered that the threat actors created a site that impersonates the Veeam Backup and Recovery software.
Besides copying the HTML code to reproduce the genuine sites, the hackers also registered typo-squat 'lookalike' domains to further add authenticity to the malicious site.
BlackBerry previously detected the RomCom malware used in attacks against military institutions in Ukraine.
Impersonating legitimate software
The website that impersonates SolarWinds NPM delivers a trojanized version of the free trial and even links to an actual SolarWinds registration form that, if filled out by the victim, leads to being contacted by a real customer support agent.
The downloaded app, though, has been modified to include a malicious DLL that downloads and runs a copy of the RomCom RAT from the "C:\Users\user\AppData\Local\Temp\winver.dll" folder.
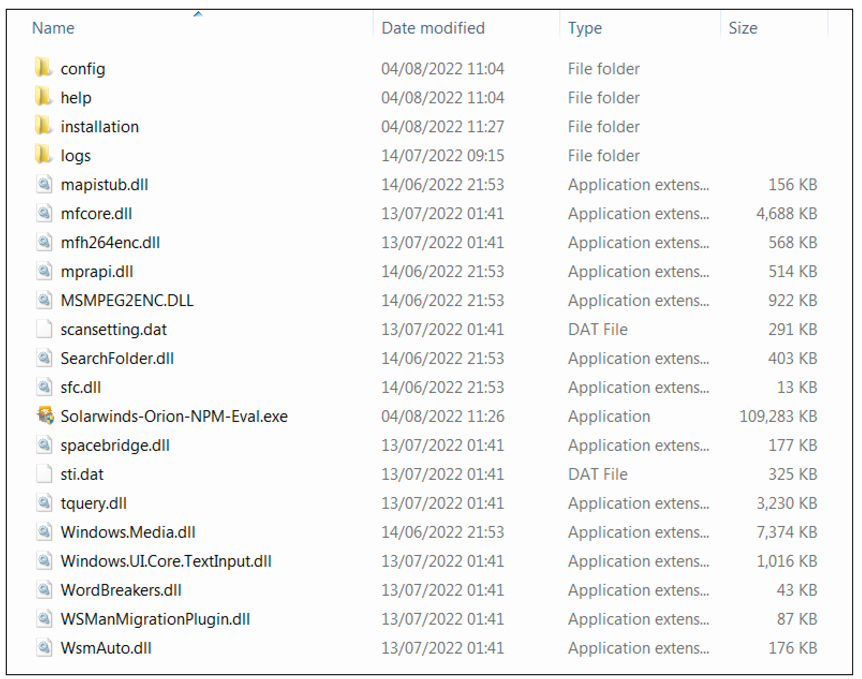
Interestingly, the downloaded executable ("Solarwinds-Orion-NPM-Eval.exe") is signed with the same digital certificate the RAT’s operators used in the Ukraine campaign, which shows the owner as "Wechapaisch Consulting & Construction Limited."
In the case of the cloned site for KeePass, which BlackBerry only discovered on November 1, 2022, the threat actors are distributing an archive named "KeePass-2.52.zip."
The ZIP file contains several files, including the "hlpr.dat," which is the RomCom RAT dropper, and "setup.exe," which launches the dropper. Setup.exe is what the user is expected to execute manually after downloading the archive.
.png)
BlackBerry’s researchers also located a second spoofed KeePass site and a PDF Reader Pro site, both using the Ukrainian language.
This indicates that while RomCom is still targeting Ukraine, they have also shifted targets to include English-speaking users.
It is unclear at this time how the threat actors are luring potential victims to the sites, but it could be through phishing, SEO poisoning, or forum/social media posts.
No attribution
In August 2022, Palo Alto Networks’ Unit 42 associated the RomCom RAT with an affiliate of the Cuba Ransomware named 'Tropical Scorpius,' as this was the first actor to employ it.
RomCom RAT was a then-unknown malware supporting ICMP-based communications and offering operators ten commands for file actions, process spawning and spoofing, data exfiltration, and launching a reverse shell.
BlackBerry’s previous report on RomCom RAT argued there was no concrete evidence pointing the operation to any known threat actors.
The new report mentions Cuba Ransomware and Industrial Spy as potentially connected to this operation; however, the motivation behind the RomCom operators still remains unclear.


Post a Comment Community Rules
You need to login in order to post a comment
Not a member yet? Register Now